
While malware is spread in abundance on the WWW, few attacks fail to hit the news. Of course, this is down to the scale of the attacks alongside, of course, the targets. I mean, the world isn’t going to stop if Little Jimmy gets a virus trying to hack free V-Bucks for Fortnite, but what about the ones that do manage to hit on a scale worthy of fear, total destruction and headline news?
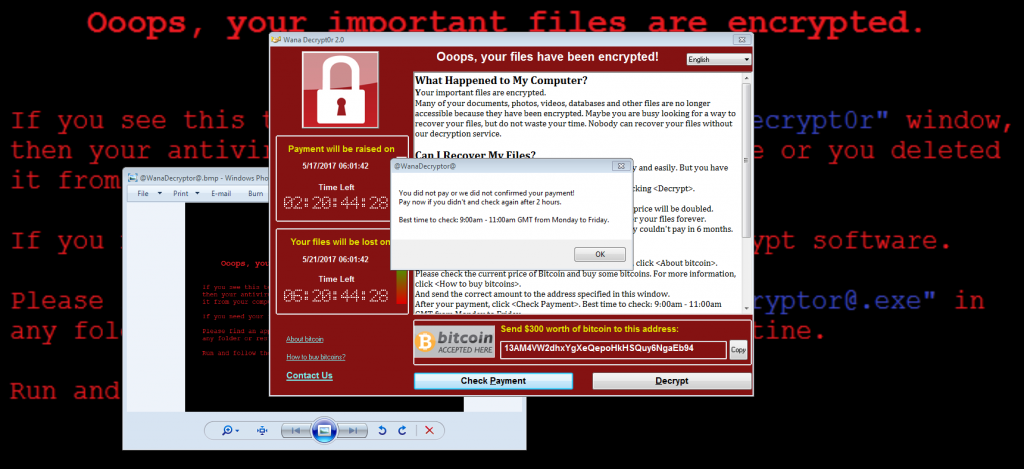
WannaCry
It was the 12th of May in 2017 when a malware attack was launched on a massive scale. So large, in fact, that at the time industry experts and malware boffins claimed that cybersecurity had changed in a way that had never before been seen.
Spreading across 300 large corporations and spanning over 150 countries, WannaCry was certainly a game changer. What made this massively destructive malware so dangerous was its sheer tenacity. Even after the virus was slowed when a kill switch was discovered, WannaCry continued on its reign of terror by infecting any computer it came into contact with.
With an estimated cost to the world of 4-billion dollars and with damage to the UK’s NHS to the tune of 90-million pounds, WannaCry is well deserving of a place on this list. Eventually, the large-scale cyber attack was tracked to the Lazarus Group – a group that worryingly had connections with North Korea.
Bad Rabbit
Bad Rabbit is notable here due to the method of infection; the Java drive-by. A Java drive-by is a method in which popular websites are taken over by by hackers who then proceed to edit the code. The edits, in this case, were made to ask website visitors to download and run an Adobe Flash update file, that was, in fact, the virus itself.

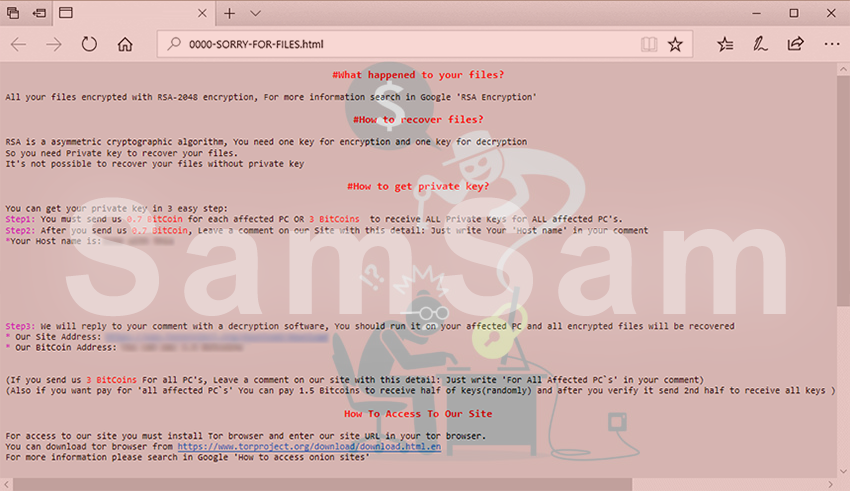
SamSam
SamSam is deserving a spot on this list due to the clever targeting of victims. The creators of SamSam only targeted those that would be most likely to pay a ransom in return for the decryption of data, mainly hospitals and educational bodies such as major universities.
Using well-known vulnerabilities, SamSam attacked networks. Once the infamous malware had done its work, the hackers were then able to elevate their access privileges to cause untold damage to their victims. Due to SamSam’s targets, larger ransoms were demanded. Consequently, the estimated blood money garnered from this infamous malware software were close to 6-million USD.
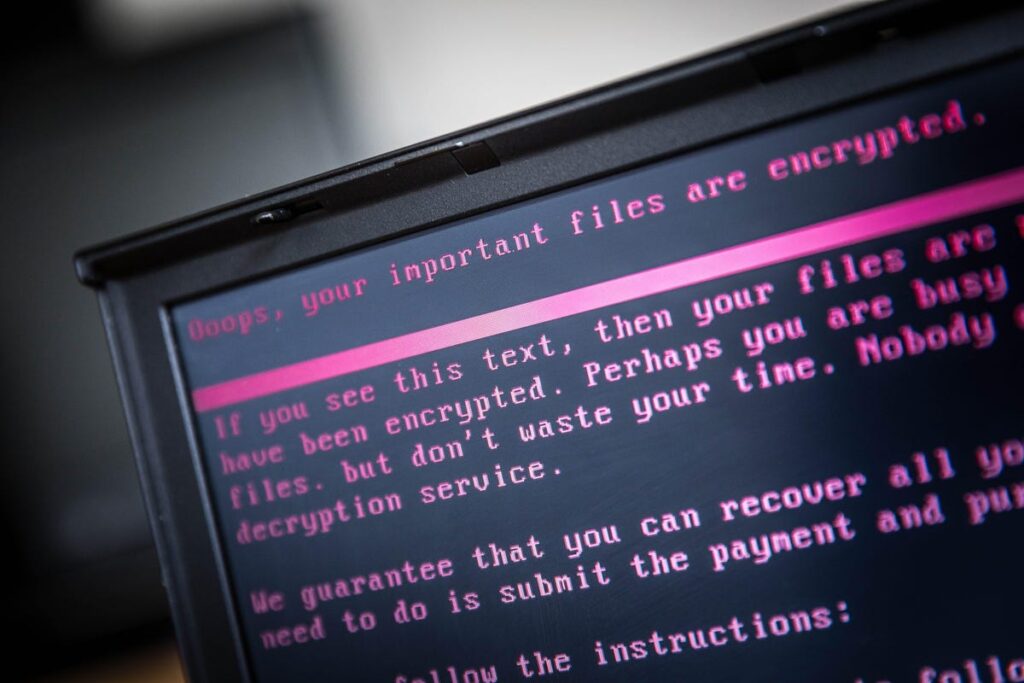
Petya
Petya was a unique ransomware, in that it encrypted the MFT (Master File Table), as opposed to the files themselves; it goes without saying that this made decryption an impossible task. Petya soon died out in 2016 but was reborn as GoldenEye just a year later.
This notorious ransomware was spread to large-scale corporations using a dummy application hosted on DropBox. GoldenEye fast became known as ‘WannaCry’s deadly sibling” and hit critical Russian targets such as banks and oil refineries. Furthermore, the malware spread to Chernobyl’s powerplant, where staff were forced to manually check radiation levels after being locked out of their operating systems.
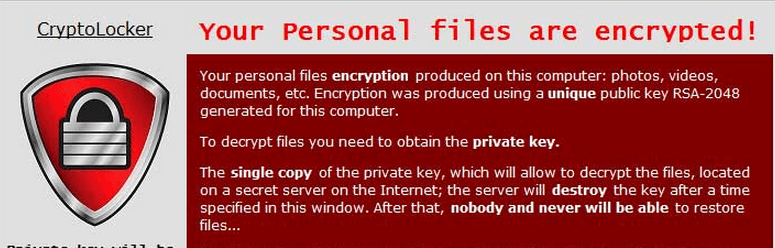
CryptoLocker
Launched at the boom of cryptocurrencies back in 2014, CryptoLocker was a ransomware tool that infected computers using phishing emails with sinister attachments. Victims were then asked to pay $400 to have the encryption taken from their personal files.
Operation Tover thankfully spelled the end for this malicious malware as the FBI, with the help of Interpol, swooped in and put an end to the attack.
Summary
What we have seen here is the devastating power that malware can have when launched on such a large scale. The attacks don’t just affect Joe Public but also have crippling consequences for vast corporations and institutions. If you fell victim to any malware attacks, listed or not; please leave a comment below.


Comments are closed.